Ill Never Buy a Google Device Again
Why Yous Should Never Use Google Authenticator Again
Reasons why U2F is meliorate than TOTP (one-time countersign)
There can never exist enough security. On the other paw, using faulty or weak protections may merely brand y'all feel safe while y'all remain exposed to various threats.
Using passwords merely is generally a bad idea, something nosotros have known since the beginning of the Internet. Nosotros are making progress toward a password-gratis world, just in the concurrently, many websites offer an boosted user business relationship protection with Two-Factor Hallmark (2FA).
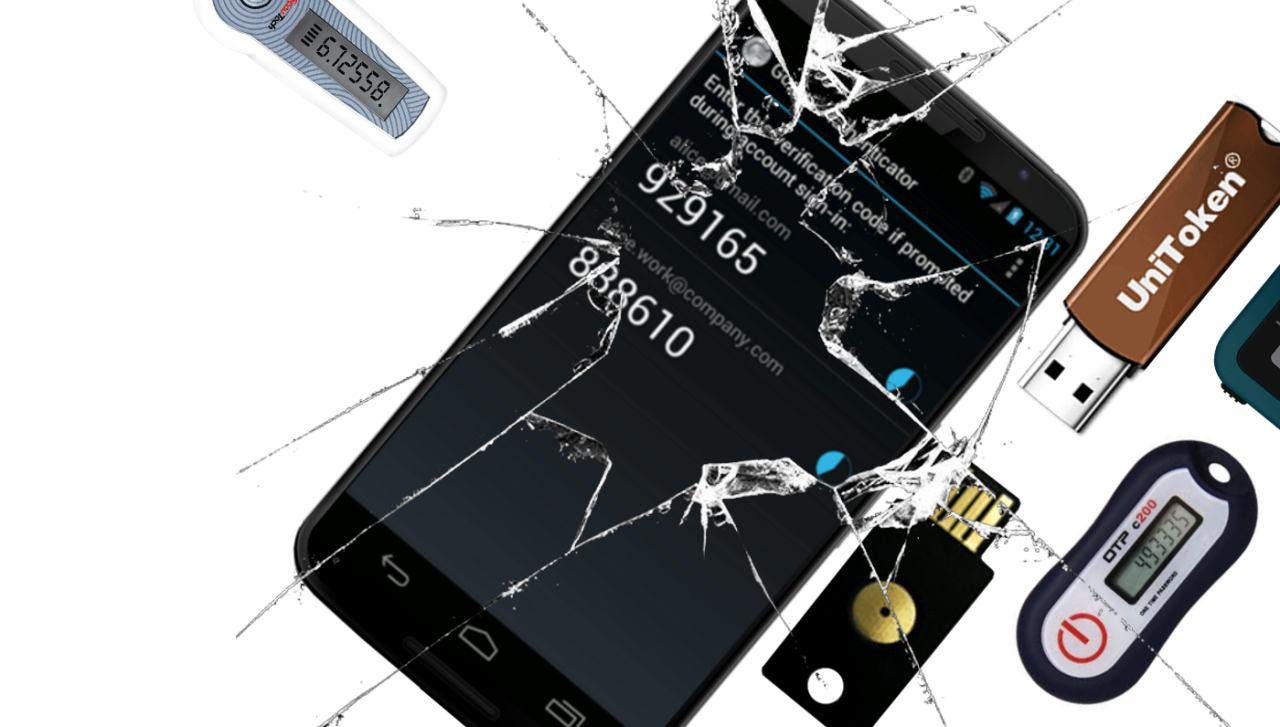
In full general, there are ii types of 2FA implementations: Fourth dimension-based Ane-time Password (TOTP) and Universal 2d Gene (U2F). Yous may be familiar with the quondam, equally it is the most ordinarily used 2FA: at login, you have to enter a ane-time code generated by your phone app, a dedicated hardware device, or sent to yous via SMS. While simple, at that place are several shortcomings to this method.
How Does TOTP Piece of work?
Time-based Old Countersign (TOTP), popularized mainly by Google Authenticator, verifies your identity based on a shared hole-and-corner. This secret must be shared online between y'all and the provider.
When logging into a website, your device generates a unique code based on the shared surreptitious and the current fourth dimension. Then y'all accept to submit this code manually. The server generates the exact aforementioned affair, based on the same secret, to compare and validate the login request.
Why Is TOTP Inadequate?
While TOTP is very simple to use, it has weaknesses and inconveniences.
- You take to manually input the lawmaking at logging in, adding another step to the process.
- Fill-in is cumbersome. You accept to take additional steps to back up the secret. Also, the services frequently offering reserve codes instead of explicitly suggesting to save the secret. If you lose your secret and log in with a reserve code, y'all will have to redo the entire TOTP registration process again.
- Backup codes are sent online, which is oft insecure.
- Yous and Provider share the same secret. If an attacker hacks into a company and gains access to both the password and the secrets database, he/she volition be able to admission every business relationship completely unnoticed.
- The secret is displayed in plaintext or QR code. It cannot be provided as a hash or with a cryptographic salt. This also means that the secret is near likely stored in plaintext form, on the servers of the provider.
- The secret can be exposed during the registration, as the provider has to give you lot a generated secret. By using TOTP, you have to trust the providers to be able to protect the secret. But tin can you?
How Does FIDO/U2F Work?
The U2F standard by the FIDO Alliance was created by technological corporations, such as Google and Microsoft, recognizing the weaknesses of TOTP. U2F uses public-key cryptography to verify your identity (Reddit — Explain Like I'chiliad Five). In contrast to TOTP, you are the but one to know the secret ( the private central ).
Benefits of U2F
- No shared undercover (private key) is sent over the internet at any time. No confidential data will always exist shared, thanks to public-key cryptography.
- Easier to use. No retyping of one-fourth dimension codes involved.
- Privacy. No personal information is associated with the secret.
- Backup is theoretically easier. Though, not ever possible. Eastward.g., you cannot support a Yubikey.
Because with U2F, there is no hole-and-corner shared and no confidential databases stored by the provider, a hacker cannot simply steal the unabridged databases to get access. Instead, he has to target individual users, and that is much more costly and time-consuming.
Moreover, y'all can back up your secret (private central). On the i mitt, it makes yous responsible for your security, merely information technology also means that y'all do not need to trust any company to protect your secrets (private keys).
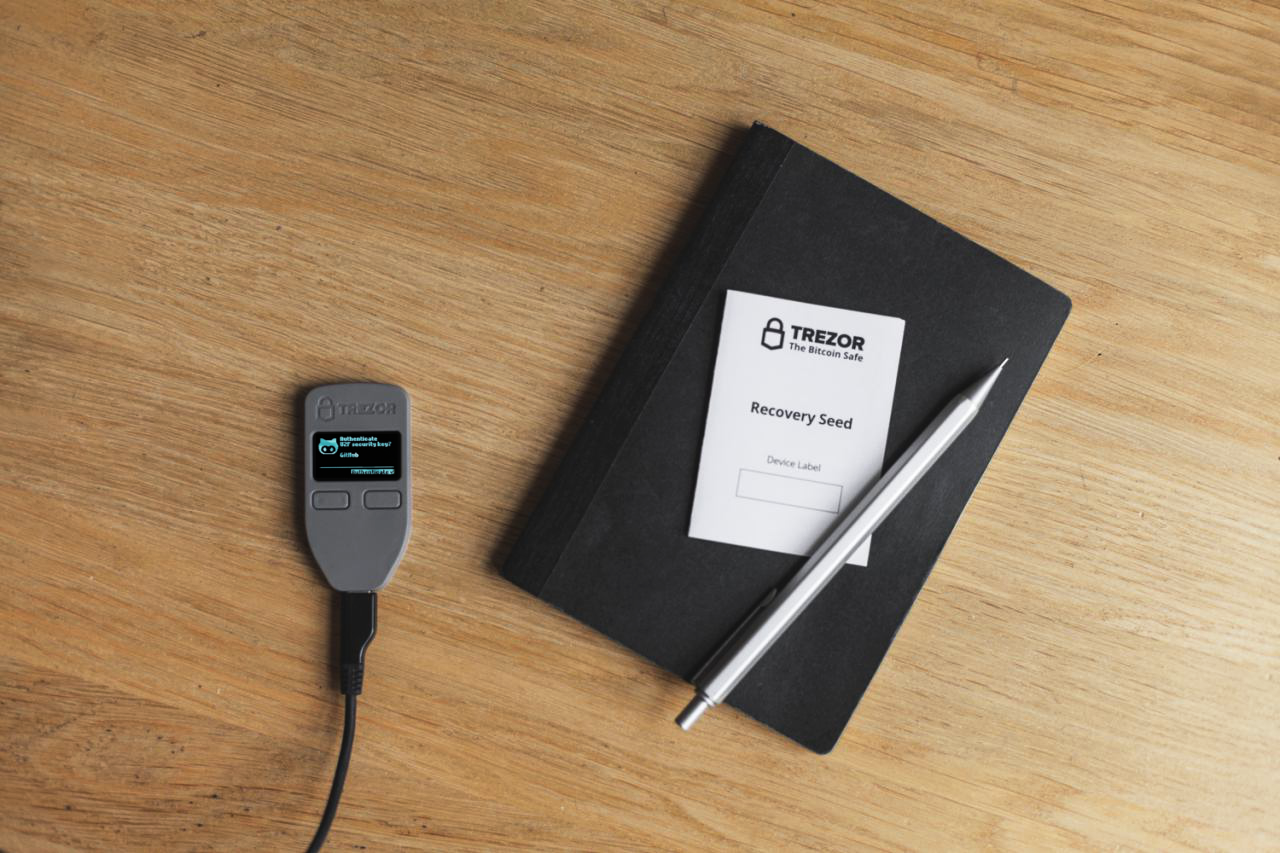
Trezor — U2F Done Right
Trezor is a small dedicated device designed to store individual keys and to serve every bit an isolated computing environment. Originally invented equally a secure Bitcoin hardware wallet, created to protect money, its uses accept expanded thanks to the wide applicability of asymmetric cryptography. Trezor can now serve as a hardware security token for U2F, but with backup/recovery functions and convenience, which no other production tin compare to.
How Does U2F With Trezor Work?
When logging into a website, y'all by and large authenticate yourself by providing a user name and a countersign. With Trezor and U2F, yous will take to additionally ostend the login with a click on your Trezor device.
Unlike some other tokens, Trezor e'er uses a unique signature for each and every user account registered. Additionally, Trezor brings U2F to a completely new level:
- Easy to support and recover. Trezor requires you to support your so-called recovery seed during the initial setup of the device. This is a sometime process for all functions of the device. The recovery seed represents all the secrets (private keys) generated past the device and can be used to restore your hardware wallet at whatever time.
- An unlimited number of U2F identities, that are all saved under ane backup.
- The secret is safely stored within Trezor. It will never be shared, equally it tin can never get out the device. No viruses or hackers can access them.
- Phishing protection with on-screen verification. Trezor always displays the URL of the website you lot are logging into, and what exactly you are virtually to authorize. You tin verify that what was sent into the device is, in fact, what you expected.
- Additional information on setup, use, and recovery of Trezor for U2F can be found in our blog mail service here or in the User Manual.
The safe characteristics of asymmetric cryptography fall into the security philosophy of Trezor. With the U2F back up in Trezor, we encourage users to use all measures available to secure their accounts and identity online.
Interesting Manufactures:
Here'southward How an Attacker Can Bypass Your Two-Factor Hallmark
Adding a phone number to your Google account can make it LESS secure
Centralized versus Decentralized Networks
About United states of america
Created by SatoshiLabs in 2014, the Trezor One is the original and most trusted hardware wallet in the world. Information technology offers unmatched security for cryptocurrencies, password management, and serves as the second factor in Two-Factor Authentication. These features combine with an interface that is easy to utilize whether you are a security expert or a brand new user.
Trezor Model T is the side by side-generation hardware wallet, designed with the benefits of the original Trezor in mind, combined with a modern and intuitive interface for improved user experience and security. It features a touchscreen, faster processor, and advanced coin support, as well as all the features of the Trezor One.

Source: https://blog.trezor.io/why-you-should-never-use-google-authenticator-again-e166d09d4324
0 Response to "Ill Never Buy a Google Device Again"
Post a Comment